Preventing Intellectual Property (IP) theft is a growing security concern for companies. From hacktivist groups to competing firms, malicious actors increasingly aim to steal sensitive information for self-gain. Besides the financial loss that could result from intellectual property being stolen, the attack could also have a devastating effect on a firm’s brand reputation.
While every company is fair game to cybercriminals, the industrial sector is especially vulnerable to IP theft as manufacturers rapidly digitize their operations. To help industrial companies understand the current IP theft situation and to curb the growing cybersecurity threat, this article will discuss the following key points:
- What Is Intellectual Property Theft?
- Who Are the Perpetrators of Intellectual Property Theft?
- Costs of IP Theft
- How Intellectual Property Is Stolen
- How to Prevent Intellectual Property Theft in Industry
What Is Intellectual Property Theft?
Intellectual property theft refers to a hostile entity stealing a company’s or an individual’s ideas, inventions, creative expressions, trade secrets, patents, copyrights, or other intellectual property. The attacker typically uses stolen IP for financial or competitive gain.
Intellectual property is like the DNA of a brand, encompassing the company’s collective knowledge, competencies, visions, etc. When your IP is robbed, someone else can use it to hold your firm ransom, or another company may gain a competitive edge.
Who Are the Perpetrators of Intellectual Property Theft?
IP theft is carried out by two general perpetrators: internal threats and external threats.
Internal Threats
Internal threats to intellectual property originate from within an organization. That could include current and former employees, contractors, and business partners. Whereas employee negligence can unintentionally lead to IP theft, corporate thieves and disgruntled employees are deliberate in their actions. They aim to steal trade secrets, design blueprints, strategic corporate decisions, and other intellectual property.
After talking to various industry actors, it’s clear that insider intellectual property threats are a big worry. Workers are increasingly relocating and jumping jobs, increasing the number of people accessing sensitive IP.
A well-known example of IP theft is when U.S. drugmaker Pfizer’s German partner BioNTech was infiltrated. Pfizer sued an employee who was in the process of leaving for another company after she stole a multitude of confidential documents. Some of the stolen intellectual property was related to the company’s COVID-19 vaccine development. Allegedly, the ex-employee uploaded more than 12,000 files without having consent to do so. She could have used these trade secrets at her new company if not caught.
External Threats
External threats to intellectual property refer to outside actors, such as cybercriminals, competition-supported malicious actors, nation state-backed attackers, and hacktivists. Most of these groups’ intentions are financially motivated, but hacktivists are usually more interested in tarnishing a firm’s reputation through theft.
Nation state-backed IP theft is a significant threat to intellectual property, as other nations continuously aim to become more economically powerful. By stealing trade secrets and various technological know-how, state-sponsored IP theft can potentially benefit a government’s modernization goals.
A recent example of intellectual property theft from an outside source is Acer. The Taiwan-based electronics maker reported that its intellectual property was compromised in a data breach carried out by a hacker. Allegedly, the hacker gained unauthorized access to one of Acer’s document servers for repair technicians.
Shortly after the mid-February 2023 cyberattack, the hacker sold the IP data on an underground forum. In total, roughly 160 Gigabytes (GB) of data were stolen in the IP attack, including 2,869 files and 655 directories.
Costs of IP Theft
Putting an exact figure on the cost of intellectual property theft is difficult, but some estimates exist. In its most recent report, the Commission on the Theft of American Intellectual Property stated that the theft of trade secrets costs the U.S. economy between 1% and 3% of its Gross Domestic Product (GDP).
That translates to between US$180 billion and US$540 billion annually.
Besides the economic toll, IP theft is also known to affect more than 45 million jobs in the United States alone.
In Europe, the European Union Intellectual Property Office (EUIPO) estimates that counterfeit products cost companies €60 billion every year. In other words, 7.5% of all sales made in the European Union (EU) involve fake products.
How Intellectual Property Is Stolen
ABI Research has identified three major areas of the manufacturing process that are the most vulnerable to intellectual property theft. Those areas are at the design stage, during production, and in post-production in the market.
- At the Design Stage: A report from Recorded Future stated that at least eight cyber espionage attacks were experienced in the semiconductor industry in 2022. This epitomizes the growing threat to intellectual property, notably project and design files, in industries with capital- and IP-intense investments. In additive manufacturing, for example, digital design files could be stolen, leaked, or intercepted as the manufacturer shares them over the cloud. As a result, the malicious actor could then create a counterfeit via Three-Dimensional (3D) printing. And unfortunately, copyright laws and IP policing aren’t enough to prevent theft. This means companies must develop better protections.
- During Manufacturing: By 2026, there will be more than 1 billion Internet of Things (IoT) connections in manufacturing environments—highlighting the expansion to Industry 4.0. But more industrial IP security vulnerabilities come with a more connected manufacturing plant and supply chain. This especially rings true when the industrial supply chain is extended, such as in contract manufacturing.
- Post-Manufacturing: Once a product is manufactured, industrial intellectual property is still unsafe. The primary danger to intellectual property in the post-manufacturing stage comes in the form of reverse engineering, cloning, and copying produced goods. To do this, a cybercriminal aims to understand how a product is designed or how a specific technology works. Reverse engineering, cloning, and copying products require the actor to study the various components and functions of the design or gain entry to proprietary secure codes or algorithms.
How to Prevent Intellectual Property Theft in Industry
This section will teach you four best practices for preventing industrial intellectual property theft.
1. Use Blockchain Technologies
At the design and planning stage, blockchain hashes and tokenization are promising solutions to secure industrial intellectual property.
With hashing, a unique fingerprint is required to access a digital 3D printable file and its contents. That way, if someone breaches the IP, a new hash will result and the organization will be alerted of infringement. Moreover, the 3D printer must encrypt the files via hashing before manufacturing them.
Additionally, industrial blockchain technologies and tokens dependent on hashes can also help avoid intellectual property theft by requiring a token for each print. In this regard, only the owner of the proprietary design controls the prints. At the same time, the manufacturer dodges the legal risk of leaked or intercepted files.
2. Re-Think IP Ownership
At the manufacturing level, IP theft can be avoided with some strategic moves related to business partners.
For one, if a manufacturer relies on third-party contractors, they can use a “build-to-specification” scheme instead of a “built-to-print.” Doing so will prevent the hiring company from accruing IP liabilities and shift the burden to the contract manufacturer.
Manufacturing companies that outsource production should weigh their options regarding IP ownership. Is it more viable to invest in your own designs, assembly drawings, and manufacturing instructions and hold ownership of the IP? Or does it make more sense to pay more for a contractor that manages the intellectual property and, therefore, distances you from IP security management?
The answer surely requires a thorough evaluation of potential suppliers and the level of trust you have in them.
3. Balance In-House IP with Supplier IP
Staying at the manufacturing level, IP theft runs rampant in industrial work settings where sophisticated molds are used for the production phase, such as plastics manufacturing. Some industrial companies take a similar approach to the electronics manufacturing industry to mitigate IP theft.
Electronics manufacturers outsource low-quality mold production to third-party vendors, such as those in China, while IP-intensive designs are developed internally. By deploying this hybrid model, so to speak, any potential breach of a third-party partner’s intellectual property will inflict considerably less damage on the brand.
Manufacturers should also be mindful of IP issues from fake products entering the production process. To combat this, companies can invest in a range of anti-counterfeiting technologies, including the following:
- DNA and glue coding
- Laser engraving of parts
- Security threads
- Anti-alteration devices
- Radio Frequency Identification (RFID)
4. Go Beyond IP Legal Venues
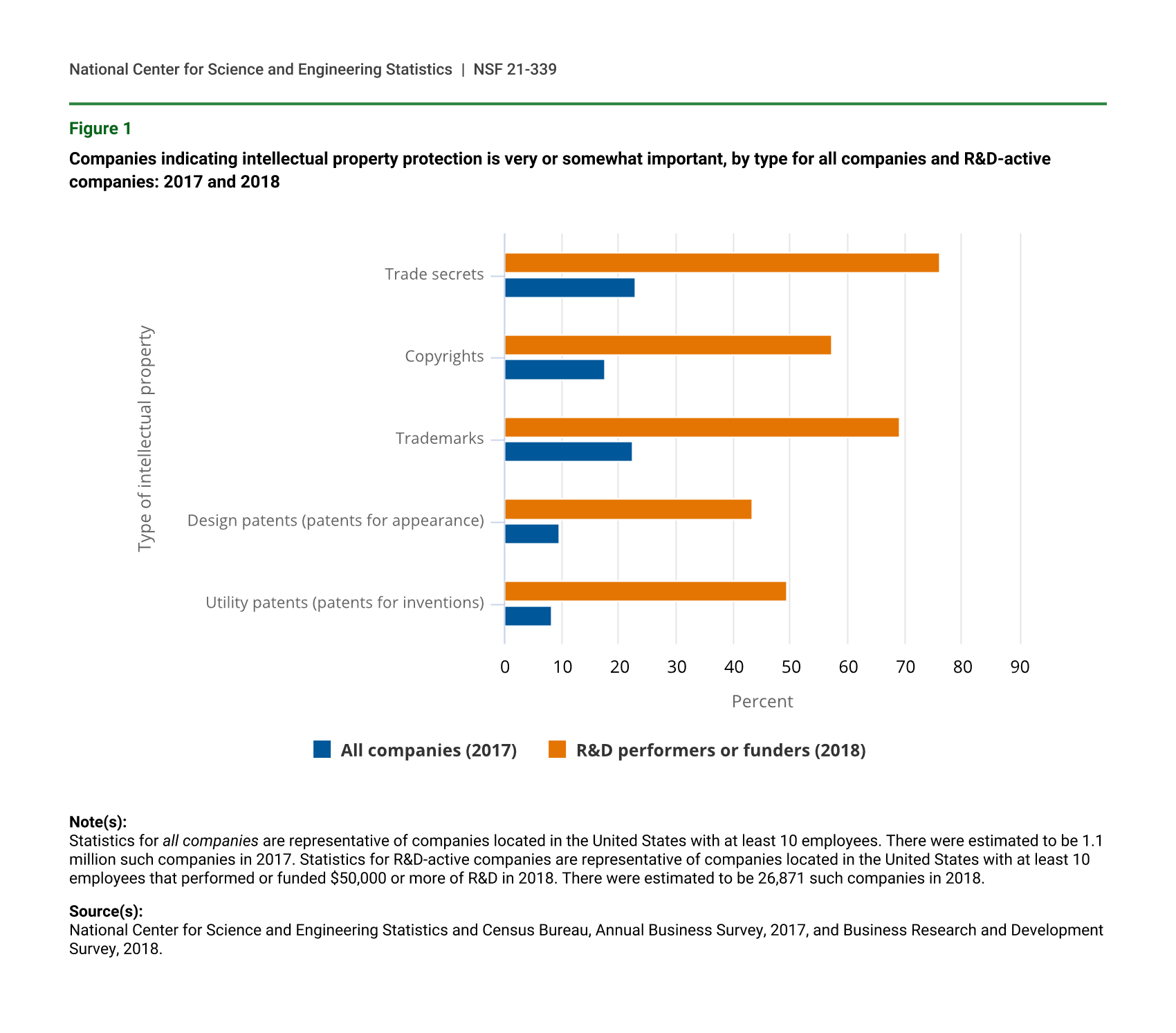
Most companies circumvent reversed engineering by maintaining patents and trade secrets. In regions where IP laws are enforced, registered patents work well. But in markets where IP infringement prevalence is high, trade secrets are the better option to prevent the theft of sensitive information.
But patent and trade secret licenses aren’t bulletproof when it comes to IP theft, particularly in adversarial geolocations. Two solutions that can bolster IP security further are confidential computing strategies and authentication Integrated Circuits (ICs).
- Confidential Computing: Digital technology IP especially benefits from confidential computing. This approach protects data using a Trusted Execution Environment (TEE) within a protected Central Processing Unit (CPU). As a result, confidential computing safeguards business logics, algorithms, and analytics functions.
- Authentication ICs: This form of cryptographic verification is often used in printers. In this scenario, an embedded IC ensures the machine only functions with authentic ink cartridges. IP tamper-resistant solutions, such as Rambus’ CryptoFirewall anti-counterfeiting system, help printer manufacturing companies avoid having counterfeit ink cartridges work.
IP Security Starts with the Right Technology Solutions
Manufacturers will continue to be a prime target for cybercriminals, necessitating industrial companies to deploy heaps of legal and technical strategies that make themselves resistant to intellectual property attacks. However, a malicious actor with enough motivation can still steal sensitive IP.
Innovative security technologies and forward-thinking strategies will be vital to keeping industrial intellectual property safe and secure from the bad guys, especially with the massive shortages in cybersecurity professionals.
To gain more knowledge on the industrial IP threat landscape, read the Shielding Intellectual Property from Cybercriminals with Industrial Data Security Research Highlight. The resource explains some more ways manufacturers can prevent intellectual property theft and the role of cybersecurity vendors and manufacturing partners in safeguarding industrial IP.



 Aisling Dawson
Aisling Dawson
 Michela Menting
Michela Menting