By Michael M. Amiri | 4Q 2022 | IN-6720
Registered users can unlock up to five pieces of premium content each month.
Cyberattacks as Tools of Punishment |
NEWS |
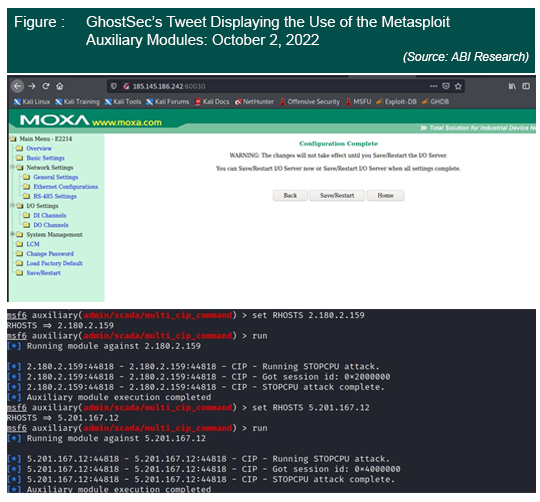
Following the tragic death of 22-year-old Mahsa Amini by police for wearing her hijab too loosely, hacktivist group GhostSec targeted Industrial Control Systems (ICS) in Iran last week in support of recent protests in the country. An unprecedented wave of protests against mandatory hijab laws and other social and economic grievances has resulted in amplified cyberattacks by hacktivist groups in support of the protestors and include a breach of the country’s state-run TV and a leak of contacts and emails of government authorities. The recent attack by GhostSec was aimed at ICS assets through controlling supervisory control and data acquisition modules using the Metasploit framework. The attackers deployed Kali Linux that enables modules to attack Operational Technology (OT) platforms. The group’s Twitter account confirmed that it had orchestrated a Modbus attack impacting MOXA and Programmable Logic Controllers (PLCs), destroying a host of them. Some of the companies affected are Mobinnet, ITC, Asiatech, Khalij-Fars-Online, Fanap Telecom, and Sabanet. While the companies are allegedly from the private sector, many have close ties with the government and security forces.
In the past, GhostSec has targeted PLCs located in Israel, allegedly taking control of water systems. Back in June, three Iranian steel companies were attacked by the hacktivist group “Gonjeshke Darande,” leading to footage of fires, damaged equipment, and halted operations at the Khuzestan Steel Company. Another hacktivist group Anonymous OpIran threatened it would target any company that has dealings with the Iranian government.
Malicious Actors Imitating ICS Hacktivist Attacks |
IMPACT |
Major ongoing geopolitical incidents around the world—including Russia’s war in Ukraine, increasing protest movements in Iran, and an acceleration in environmental activism—will lead to a spike in hacktivist attacks. Many of these groups are highly motivated entities whose successful campaigns could be imitated by bad actors seeking financial gains from similar attacks. Since OT systems control physical functions, malicious actors can weaponize them to harm or even kill humans. The cost of such attacks is immense and could result in irreparable brand damage. While ransomware attacks are for monetary gain, and while the parties involved might decide to resolve matters discreetly, hacktivists will be sure to reveal and amplify the damages, leading to reputational risks for firms.
Attackers will target different sectors but will increasingly choose visible and salient industries that can deliver more funds to malicious actors or that will result in increased recognition for hacktivists, such as critical infrastructure and heavy industries. As the GhostSec attack demonstrates, PLCs, human-machine interfaces, and other ICS equipment are receiving increased attention both from cyberattackers and security vendors. The attacks compliment reports that industrial cyberattacks represented 23.2% of such incidents in 2021, the highest of any category, including finance. ABI Research forecasts that ICS cybersecurity revenue will display a 23% total increase in the 2019–2024 period, revealing the increasing importance of threats to ICS operators and underlying the demand to mitigate damages.
Mitigating Growing Threats |
RECOMMENDATIONS |
While the attack was targeted at companies that are close to a government with a proven track record in malicious cyberactivity, it is another sign that ICS cybersecurity is severely lacking. Most current ICS technology was designed 20 years ago when cybersecurity tools were not inserted in systems, making them prone to threats. Industrial firms should be especially vigilant at times of heightened socioeconomic tensions as the threats of unpreparedness expose these firms to more risk. Companies with government contracts or those deemed as contributing to grievances are prime targets. The cyber breach also indicates that the advent of the industrial Internet of things could cause major issues for current and future infrastructure investments.
Companies with direct Internet access to their OT equipment should be especially vigilant and take appropriate measures. This includes changing and strengthening default system passwords, taking advantage of multifactor authentication for external facing systems, and keeping ICS firmware up to date. Vendors can benefit from established ICS security frameworks, such as the NIST 800-82’s Guide to Industrial Control Systems Security and the ISA 99.02.01/IEC 62443 Security for Industrial Automation and Control Systems.